From hidden notes to cryptic ciphers, history is filled with stories of secret codes – but it’s not just spies who use covert methods to keep secrets concealed.
Here, Mark Frary, co-author of The Story of Codes, tells Sam Boemi the Honest Truth about encryption in everyday life.
What first made you interested in researching how codes have been used in history?
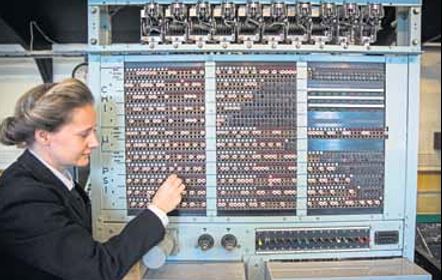
I have been interested in codes ever since I was a child. I used to love cracking the codes in puzzle magazines on long car journeys. I have been writing about science and technology ever since university when I studied astronomy and physics. I now live close to the Bletchley Park codebreaking centre, and it has always had a fascination for me, so writing a book about it seemed like an obvious thing to do. To write a book with my friend and fellow science writer Stephen Pincock seemed like an even better idea — we had lots of fun researching it.
How did the Zimmerman Telegram change the course of the First World War?
In 1917, a team of British codebreakers from the secret “Room 40” intercepted a telegram sent by the German Foreign Secretary, Arthur Zimmerman, to the country’s ambassador to Mexico. The coded message promised that if Mexico became a German ally and they won the war Mexico would be handed back the territories of Texas, New Mexico and Arizona. The British faced a dilemma. If they revealed the contents of the message to the US, it would reveal to the Germans their cipher had been broken. Luckily, another copy of the message that used an already broken cipher was found in a telegraph office. Its contents were made known to the Americans, who declared war on Germany and its allies shortly afterwards.
Codes and ciphers can be dated all the way back to ancient Egypt. Why did stonemasons use altered hieroglyphs?
Some 4,000 years ago, Egyptian scribes carving histories into the rock of great monuments began to subtly alter the hieroglyphics. Over the next four millennia, politicians, military leaders, business people and star-crossed lovers began to realise they could hide their messages by using codes to stop people learning their innermost secrets.
What are some easy codes we can make ourselves?
A substitution cipher is a simple one to use. Write down the letters of the alphabet in a row. Underneath each letter, write a letter (or even draw a symbol) that will represent that letter in your code, making sure you don’t repeat yourself.
In your message, replace each letter with the one below it in the coding table.
Send the coded message to the recipient and then, separately to foil would-be spies, the coding table.
They just do the procedure in reverse to reveal the message.
Do you have a favourite code you use yourself?
Whenever I am signing books, I use the Caesar cipher to write a coded message for the person buying the book.
Julius Caesar used this simple method to hide his messages — you just shift all of the letters of the alphabet a fixed number of places. For example with a shift of three, A becomes D, B becomes E, C becomes F and so on. Using this cipher, Sunday Post becomes Vxqgdb Srvw.
Do personal ads use codes?
Young lovers of the late Victorian era would often share coded messages through the personal columns of newspapers. Lyon Playfair, first Baron Playfair of St Andrews, and his great friend, the scientist Charles Wheatstone, loved trying to crack the messages. On one occasion, Wheatstone and Playfair unravelled the messages being sent between an Oxford student and his sweetheart. When the student suggested elopement, Wheatstone took matters into his own hands, placing an advertisement of his own in the couple’s cipher, urging them to abandon their foolhardy plan. Soon there followed another message: Dear Charlie: Write no more. Our cipher is discovered!
The Story of Codes, published in hardback by Modern Books, is out now
Enjoy the convenience of having The Sunday Post delivered as a digital ePaper straight to your smartphone, tablet or computer.
Subscribe for only £5.49 a month and enjoy all the benefits of the printed paper as a digital replica.
Subscribe