
Cybercriminals find new and innovative ways to steal everything from personal information to bank account details. But just how did the internet become a home for hackers?
Here, author and journalist Geoff White tells Alice Hinds the Honest Truth about the history of hacking:
How much do cybercriminals steal each year?
Cybercrime now accounts for more than half of all criminal offences in the UK, and Get Safe Online, a UK Government-backed advice service, says cyber fraud costs businesses more than £1billion every year.
Why is the collapse of the USSR linked to a rise in cybercrime?
The Soviet Union had a long history of promoting science and technology, and by the ’90s millions of its youngsters were studying tech and engineering. But as its economy flatlined after the break-up of the USSR, those tech-savvy youngsters often struggled to get suitable jobs. At the same time, online commerce was booming, and security was still playing catch-up. And so, a small minority of youngsters turned to cybercrime.
What was the Bulletin Board System? And why was it important for the spread of hacking?
The Bulletin Board System (BBS) was an early form of online chat. Users could leave messages and response to others’ posts and it was where the first techies hung out, so a lot of early hackers swapped knowledge. In those days there wasn’t much money to be made from cybercrime, but BBS was where the spirit of hacking was first thrashed out.
Why was musician John Perry Barlow visited by the FBI during online crime investigations?
Barlow was the lyricist for hippie group The Grateful Dead, and an early fan of BBS life. When an electronic file was stolen from Apple, Barlow came under suspicion. An FBI agent visited his ranch in 1990, and Barlow recounts the bizarre experience of having to explain to the agent the basics of the very computer technology the agent was supposed to be investigating. “You know things have rather jumped the groove when the potential suspects must explain to law enforcers the nature of their alleged perpetrations”, Barlow later wrote.
Has the invention of online currency Bitcoin enabled more hacks to take place?
There’s no question that Bitcoin, a radical new form of digital money, has fuelled a large amount of cybercrime. Early on, it was the currency of the “dark web”, a hidden network rife with criminality. Bitcoin has also enabled hackers to launch ransomware, in which victims’ files are scrambled, and they’re then charged a ransom (usually in Bitcoin) to recover them.
People think of cybercriminals only attacking bank accounts and emails – but is it true hackers could bring down the electrical grid?
Sadly, yes. In 2015 and 2016, hackers cut power to hundreds of thousands of homes in Ukraine, in attacks on its electricity distributors.
It happened in the middle of a conflict with Russia, leading many to suspect Kremlin hackers were behind it – accusations Russia has denied. Cybersecurity firms have discovered criminals targeting the UK’s energy network, hacking into companies who supply the industry with kit and personnel. There’s no suggestion the UK was on the verge of being plunged into darkness, but it’s a worrying new frontline in the cyber battle.
Any particularly memorable factoids you discovered?
Tom Cruise inadvertently sparked a cyberwar!
The Hollywood actor was well known as a scientologist, and a video was leaked in which he talked about the religion in seemingly bizarre terms. The Church of Scientology tried to stop the video being published online. The Anonymous hacking movement (the folks who often wear Guy Fawkes masks) saw that as censorship, something they vehemently disagreed with. So, they attacked the Church of Scientology, which was predictably robust in its response…
Crime Dot Com: From Viruses To Vote Rigging, How Hacking Went Global by Geoff White, Reaktion Books, £18.99, is out now
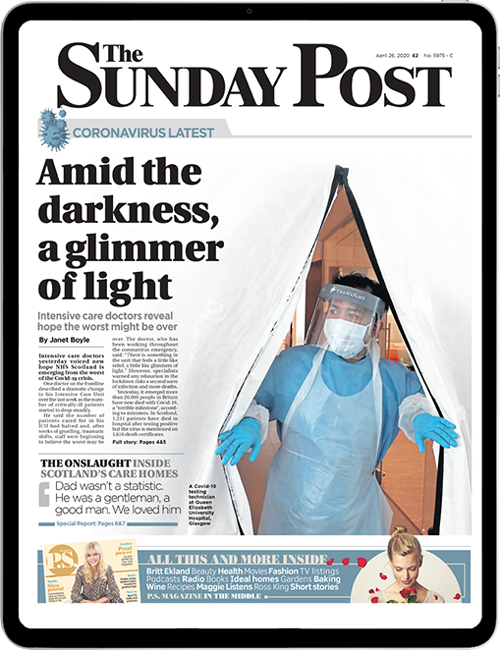
Enjoy the convenience of having The Sunday Post delivered as a digital ePaper straight to your smartphone, tablet or computer.
Subscribe for only £5.49 a month and enjoy all the benefits of the printed paper as a digital replica.
Subscribe